

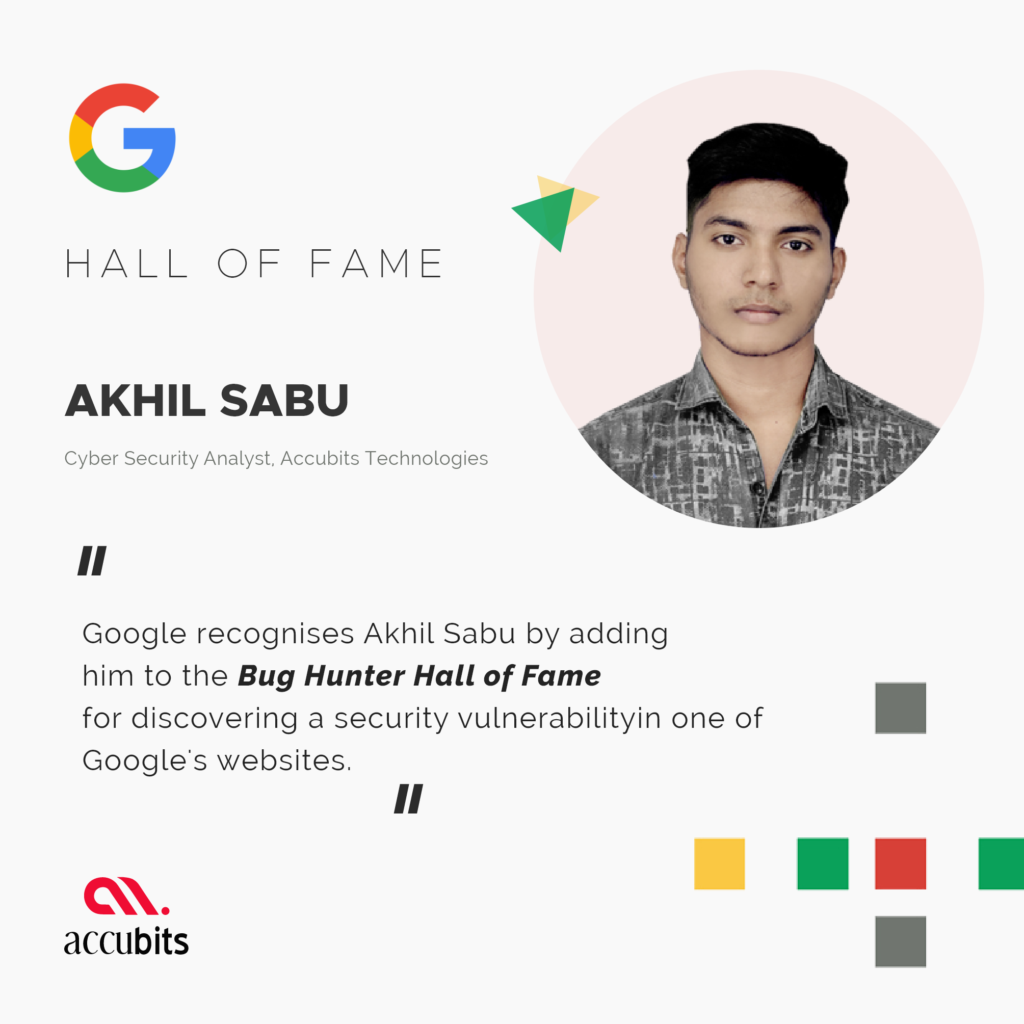
Google’s products and services are currently being used by billions of people all over the world. This is why any kind of security threat can have extremely severe consequences. Akhil Sabu, a cybersecurity analyst at Accubits Technologies discovered a security bug in one of Google’s applications and was enlisted in Google’s Hall of Fame when he reported it.
Akhil Sabu recognized a subdomain takeover vulnerability in one of Google’s applications. This would allow an attacker to set up a page on the service that was being used and point their page to that subdomain and claim it as their own. Sabu has been participating in such bug bounty programs since his college days and has been featured in the Hall of Fame of various other organizations like Inflectra, Indeed, and the University of Victoria.
In November 2010, Google launched a Vulnerability Reward Program for Google-owned web properties. Under the program, anyone who can identify and report any vulnerability in Google-developed apps, extensions, hardware devices, or any other web properties is eligible to receive monetary rewards for their effort. A reward panel will come to a decision on the final reward based on the severity of the issue. The company stated that they’ve received more than 8,500 vulnerability reports and paid rewards over $5 million. Any design or implementation issue that substantially affects the confidentiality or integrity of user data is likely to qualify for the program. A few examples of such vulnerabilities would be Cross-site scripting, Cross-site request forgery, Mixed-content scripts, Authentication or authorization flaws, Server-side code execution bugs, etc
Google will also feature the individual who reports the bug in its Hall of Fame. The bug reporters are ranked according to the number of valid bug reports they have sent in, the severity of the bug, how recent the report was and the amount of money contributed to charity. Akhil Sabu is working as a cybersecurity analyst at Accubits Technologies, specializing in computer and network security, vulnerability assessment, malware analysis, and Incident Response.