

This website stores cookies on your computer. These cookies are used to collect information about how you interact with our website and allow us to remember you. We use this information in order to improve and customize your browsing experience and for analytics and metrics about our visitors both on this website and other media. To find out more about the cookies we use, check our Privacy Policy
Agree & Close

We believe, we are striding into the next phase of human evolution where technology negates the human miseries and we humans can work towards sustaining humanity. We constantly focus on innovations to make this future closer to us.
Explore this whitepaper on Generative AI in Banking and Financial Services. Discover its potential to transform business and improve billions of lives.
In this whitepaper, we will explore generative AI and identify business growth opportunities it offers. We aim to provide business owners with a comprehensive guide to using AI to unlock new opportunities and achieve sustainable growth. We will explore how generative AI can be used to analyze data and identify patterns, as well as how it can be used to generate new ideas and solutions.
This Whitepaper explores Web3, a decentralized web built on blockchain technology, and its potential benefits for businesses. The benefits of transparency, security, user control, and tokenization are highlighted in the paper. To better understand the technology, it refers to Web2 and Web2.5 as predecessors to Web3. Security, privacy, and regulatory concerns are all acknowledged risks. The paper also emphasizes Web3's potential to transform industries and encourages businesses to stay ahead of the curve and embrace the Internet's future.
This whitepaper will explore the essentials for launching a successful blockchain product. In the first section, we’ll explore how to choose the right blockchain for developing your DApp. In the second section, we’ll explore the essentials for DApp development, including the best practices, methodologies, common vulnerabilities, audit process, and tools. In the final section, we’ll explore the fundamentals of token economy design for your blockchain project.
Here's a step-by-step checklist to get your e-Learning project off the ground. This guide includes technical functionalities, a feature list, and more viable information for your project.
Do you intend to create an NFT marketplace? Do you want to learn how to build an NFT marketplace platform from the ground up? Here's a handy checklist to get you started. This document contains technical specifications, a feature list, and other useful information for your NFT project.
Apple is known for its top-notch privacy and security capabilities. Apple products and services are currently being used by billions of people worldwide. Any security loopholes or threats can have extremely severe consequences. Naveen Kumar, a Security Engineer at Accubits Technologies, discovered a security bug in one of Apple’s applications and was enlisted in Apple Web Server Security Acknowledgements when he reported it.
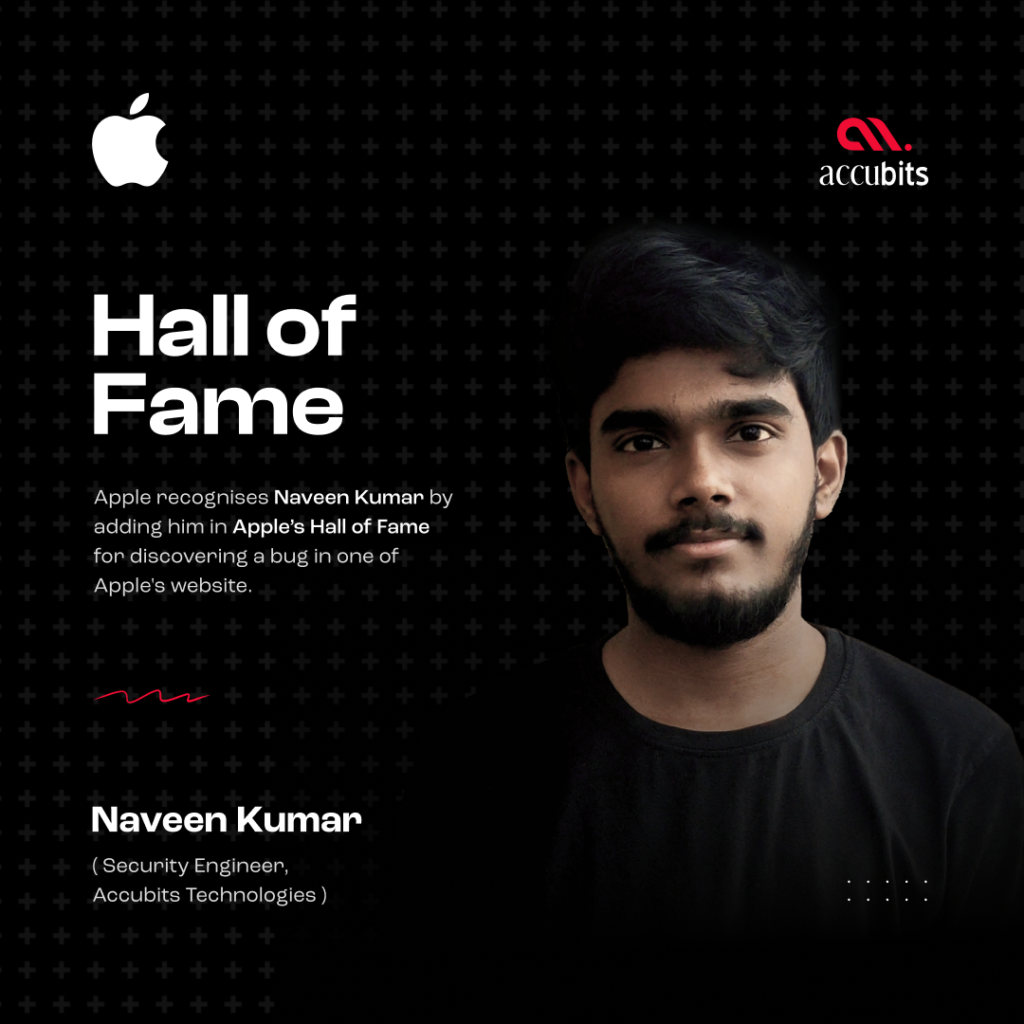
Naveen identified a subdomain security issue on one of Apple’s websites. During his research, he discovered that one subdomain was not handling errors accurately, allowing attackers to inject any text or HTML code. This vulnerability patch would allow code-based attacks like HTML injection.
Apple acknowledges the individuals who identify and report the bug in its Hall of Fame. Apple only publishes the list after addressing and solving the security issue. The bug reporters are ranked according to the number of valid bug reports they have sent in, the severity, and how recent the report was. Naveen Kumar is working as a Security Engineer at Accubits Technologies, specializing in computer and network security, vulnerability assessment, malware analysis, and Incident Response. Naveen has participated in such bug bounty programs and has been featured in the Hall of Fame of various other organizations like Google, Zoho, Mozilla, cPanel, etc.